1) Crimeware
This is designed to fraudulently obtain financial gain from either the affected user or third parties by emptying bank accounts, or trading confidential data, etc. Crimeware most often starts with advanced social engineering which results in disclosed info that leads to the crimeware being installed via programs that run on botnets which are zombie computers in distant places used to hide the fraudsters I.P (internet protocol) trail. Usually the victim does not know they have crimeware on their computer until they start to see weird bank charges or the like, or an I.T. professional points it out to them. Often times it masquerades as fake but real looking antivirus software demanding your credit card info in an effort to then commit fraud with that info.
2) Cyber-Espionage
The term generally refers to the deployment of viruses that clandestinely observe or destroy data in the computer systems of government agencies and large enterprises – unauthorized spying by computer, tablet, or phone. Antivirus maker Symantec described one noteworthy example where the U.S. Gov’t made a worm to disable Iran’s nuclear reactors arguably in the name of international security (Fig. 1).
“Stuxnet is a computer worm that targets industrial control systems that are used to monitor and control large scale industrial facilities like power plants, dams, waste processing systems and similar operations. It allows the attackers to take control of these systems without the operators knowing. This is the first attack we’ve seen that allows hackers to manipulate real-world equipment, which makes it very dangerous. It’s like nothing we’ve seen before – both in what it does, and how it came to exist. It is the first computer virus to be able to wreak havoc in the physical world. It is sophisticated, well-funded, and there are not many groups that could pull this kind of threat off. It is also the first cyberattack we’ve seen specifically targeting industrial control systems” (Accessed 03/20/16, Norton Stuxnet Review).
Richard Clarke is the former National Coordinator for Security, Infrastructure Protection and Counter-terrorism for the United States and he commentated on Stuxnet and cyber war generally in this Economist Interview from 2013.
Fig.1.
3) Denial of Service (DoS) Attacks
A DoS attack attempts to deny legitimate users access to a particular resource by exploiting bugs in a specific operating system or vulnerabilities in the TCP/IP implementation (internet protocols) via a botnet of zombie computers in remote areas (Fig. 2). This allows one host (usually a server or router) to send a flood of network traffic to another host (Fig. 3.). By flooding the network connection, the target machine is unable to process legitimate requests for data. Thus the targeted computers may crash or disconnect from the internet from resource exhaustion – consuming all bandwidth or disk space, etc (Fig. 3.). In some cases they are not very harmful, because once you restart the crashed computer everything is on track again; in other cases they can be disasters, especially when you run a corporate network or ISP (internet service provider).
Fig. 2. Fig. 3.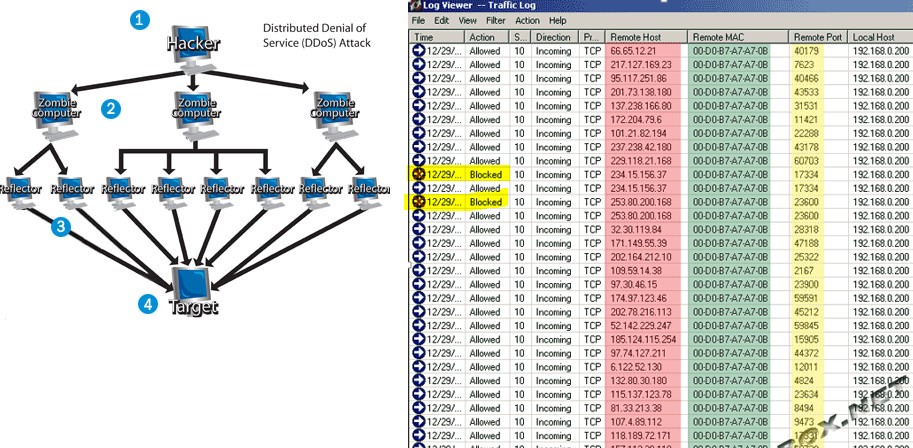
4) Insider and Privilege Misuse
Server administrators, network engineers, outsourced cloud workers, developers, I.T. security workers, and database administrators are given privileges to access many or all aspects of a company’s IT infrastructure. Companies need these privileged users because they understand source code, technical architecture, file systems and other assets that allow them to upgrade and maintain the systems; yet this presents a potential security risk.
With the ability to easily get around controls that restrict other non-privileged users they sometimes abuse what should be temporary access privileges to perform tasks. This can put customer data, corporate trade secrets, and unreleased product info at risk. Savvy companies implement multi-layered approvals, advanced usage monitoring, 2 or 3 step authentication, and a strict need to know policy with an intelligible oversight process.
5) Miscellaneous Errors
This is basically an employee or customer doing something stupid and unintentional that results in a partial or full security breach of an information asset. This does not include lost devices as that is grouped with theft – this is a smaller category. The 2014 Verizon Enterprise Data Breach Investigation Report gives an example of this category as follows:
“Misdelivery (sending paper documents or emails to the wrong recipient) is the most frequently seen error resulting in data disclosure. One of the more common examples is a mass mailing where the documents and envelopes are out of sync (off-by-one) and sensitive documents are sent to the wrong recipient” (Accessed 02/21/16, Page 29).
6) Payment Card Skimmers
This is a method where thieves steal your credit card information at the card terminals, often at bars, restaurants, gas stations, sometimes at bank ATMs, and especially where there is low light, no cameras, or anything to discourage the criminal from tampering with the card terminal.
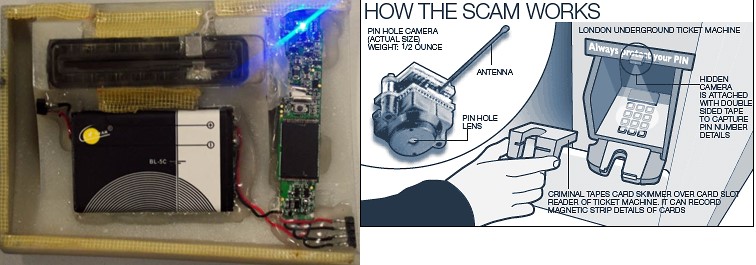
Corrupt employees can have a skimmer stashed out of sight or crooks can install hidden skimmers on a gas pump. Skimmers are small devices that can scan and save credit card data from the magnetic stripe (Fig. 4.). After the card slides through the skimmer, the data is saved, and the crooks usually then sell the information through the internet or if they really want to be secure the Darknet which is a secure non-mainstream internet that requires a special browser or plug-in to access. After this counterfeit cards are made, then bogus charges show up, and the bank eats the costs which unfortunately drives up the cost of banking for everyone else. Also, some skimmers have mini cameras which record the pin numbers typed at ATM machines for a more aggressive type of fraud (Fig. 5.). Here are two images of skimmer technologies:
Fig 4. Fig 5.
7) Physical Theft and Loss
This includes armed robbery, theft by accident, and/or any type of device or data lost. Although some of the stolen or lost items may never end up breached or used for fraud sometime they are depending on what device and/or what data is on that device and/or if it was encrypted or not, or if it the data could be deleted remotely, etc.
8) Point of Sale Intrusions
See my 2014 post on the Target Data Breach here for a good example.
9) Web App Attacks
These incidents were carried out primarily via manipulation of vulnerabilities in input validation and authentication affecting common content management systems like Joomla, Magento, SiteCore, WordPress, and Drupal.
According to the 2015 Verizon Data Breach Investigation Report these types of attacks are not only a reliable method for hackers, but also fast with 60% of the compromises taking a few minutes or less(Accessed 02/21/16). With web applications commonly serving as an organization’s public face to the Internet, the ease of exploiting web-based vulnerabilities is alarming (Accessed 02/21/16, 2015 Verizon Data Breach Investigation Report). According to The Open Web Application Security Project these are two common types Web App weaknesses (Accessed 02/21/16, 2013, OWASP 10 Most Critical Web Application Security Risks):
“i) Injection flaws, such as SQL, OS, and LDAP injection occur when untrusted data is sent to an interpreter as part of a command or query. The attacker’s hostile data can trick the interpreter into executing unintended commands or accessing data without proper authorization.
ii) XSS flaws occur whenever an application takes untrusted data and sends it to a web browser without proper validation or escaping (Fig. 6.). XSS allows attackers to execute scripts in the victim’s browser which can hijack user sessions, deface web sites, or redirect the user to malicious sites access unauthorized pages”.
Fig. 6.
Jeremy Swenson, MBA is a seasoned, Intel certified, retail technology marketing and training representatives on assignment at Best Buy for clients including Intel, Trend Micro, Adobe, and others. He also doubles as a Sr. business analyst and project management consultant. Tweet to him @jer_Swenson.

1 Comment. Leave new
Reblogged this on Brian Pennington.