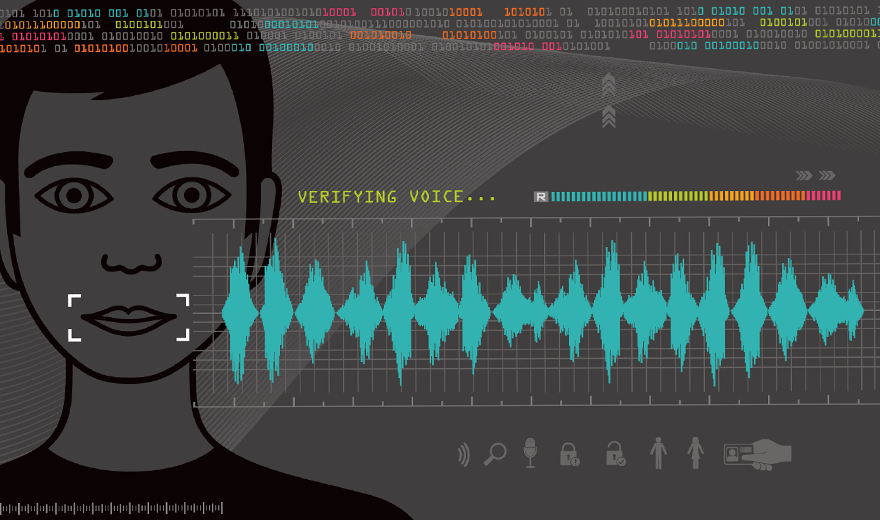
Over the last few two years, many financial firms have introduced a new voice identity and access (IAM) management service which uses voice biometrics technology to identify you by your unique voice. This starts each customer interaction with effortless biometric authentication improving customer experience.
Charles Schwab describes it this way (2020):
- Whether you want to use our automated phone service or speak with one of our financial professionals, our voice ID service is one of the fastest and most convenient ways to securely identify yourself over the phone.
- We know that you have a lot of passwords and pins to remember. Voice ID helps reduce the hassle of answering security questions when we can verify you by the sound of your voice.
- When you call us, you will simply be prompted to say the passphrase “At Schwab, my voice is my password” to be securely verified. No more personal questions. No more PINs.
According to leading voice technology vendor Nuance (2020):
- Biometric authentication delivers simpler, stronger customer authentication.
- It reduces the average handling time (AHT) by 37 seconds.
- Just like your fingerprint, your voiceprint is uniquely yours.
To make this work, the technology stores a digital representation of your voice using a proprietary algorithm. This unique voiceprint is created from more than 100 different physical and behavioral characteristics such as pitch, accent, shape of your mouth and vocal tract as you speak with a customer service representative. Your voice ID only works with the system you provide your voice to, etc.
Using this service requires the collation of data to know that you are you. Melissa Looker of Fast Company describes how Chase does this as follows (2019):
- But Chase isn’t just amassing data on its customers. It’s also collecting intel on known fraudsters for so-called “voice biometric blacklists,” which keep tabs on identity thieves and credit card scammers and prevent them from accessing bank information or requesting new credit cards.
- Of course, it’s not just JPMorgan Chase & Co. using the technology. According to the Associated Press, Wells Fargo, Barclays, and U.S. Bank all use some form of Voice ID (IAM). In 2017, Pindrop, a company that offers sound-based fraud detection tools to call centers, told Fast Company it worked with eight of the top 10 U.S. banks and two of the top 5 insurers to detect phone scams.
Although voice IAM is a good start, I think more research needs to be done to validate the long-term viability of this authentication. What if a fraudster has a recording of your voice, or can mimic your voice pattern with a computer? Also, a lot of people’s voices sound the same. According to a 2017 BBC report voice, biometric authentication was easily passed by a twin brother when they tested it, and the technology has improved little since then (Dan Simmons).