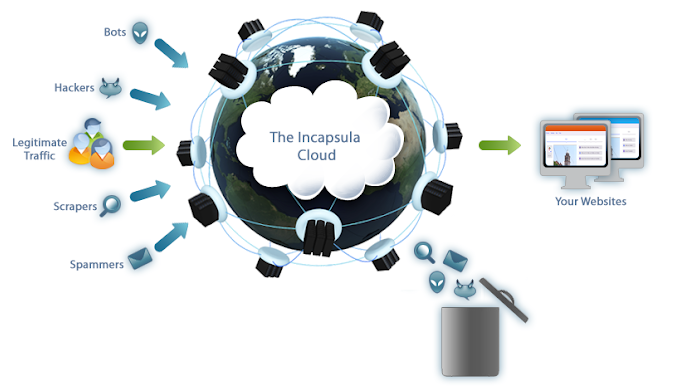
Imperva, formally Incapsula, disclosed on 08/27/19 a data breach impacting its many customers. The company focuses on cyber-security and DDoS mitigation and consulting, heavily via its cloud web application firewall (WAF).
The breach was discovered 08/20/19 via a third-party. Unfortunately, the exposure goes back to 09/15/17 which means they were compromised at least in part for more than two full years! Clearly, this is evidence of poor internal controls. The exposed data includes customer email addresses, hashed and salted passwords; and API keys and customer-provided SSL certificates — for a partial portion of the exposed data.
Don’t count on cyber security and software firms to be more secure than any other type of company. This breach is likely to negatively impact sales, product design, and will trigger a few investigations, and at least one lawsuit. Additionally, the insurance claim question is a loaded one — and is dependant on how much due diligence the company did before the breach.
To learn more about how to stop data breaches like these at your organization consider attending the Cyber Security Summit this fall.
- The Ninth Annual Cyber Security Summit, “Pushing the Cyber Security Envelope,” takes place Oct. 28-30, 2019, at the Minneapolis Convention Center in Minneapolis, Minn.
- The Summit has given awards to top leaders in industry, government and academia since 2015. However, for 2019 the awards program was expanded to include a wider array of visionaries.
- New this year, women in Cyber, PLUS 16 Tech Sessions, along with Healthcare & Med Device Cyber Security. Check out this Star Tribune piece from Summit co-chair Catharine Trebnick and colleague Kyle Bauser on this very important topic.
- To stay up to date on the Summit and top cyber security issues, follow the Cyber Security Summit on social media: Twitter, Facebook, LinkedIn, YouTube. Follow the hashtag #cybersummitMN for the latest conversations on this top matter.
As Summit co-founder Eileen Manning stresses in a well-circulated cover story for Upsize Magazine, cyber security is fundamental for small businesses that work with larger companies, which require it – not to mention for pure survival.
Data breaches like the one at Impervia are likely to increase so interested parties should come together to learn, debate, and flesh out solutions for a more secure future! Creativity focused startups are ripe for this challenge.
